Table of Contents
Links - Security
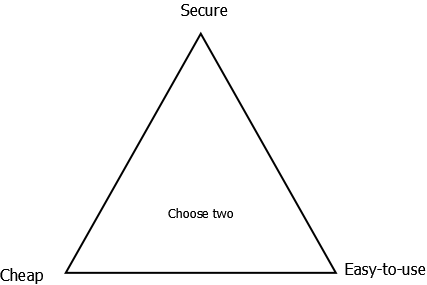
Similar to Zooko's triangle.
Security sites
US-CERT Vulnerability Notes Database
CERT
Secunia - Vulnerability and Virus Information
SecurityFocus
VulnWatch - Vulnerability Disclosure List
Computer Security News
Threat Minded
Ultimate Windows Security
Insecure.Org
Center for Internet Security
Common Criteria Portal
CVE Details provides an overview of CVEs per vendor/product. Examples:
GitHub - Distributed Weakness Filing
CVE Data Updates and RSS Feeds
NVD Data Feeds
Bruce Schneier - security technologist.
NSA Security Configuration Guides
B.I.S.S. - Bluetack Internet Security Solutions home van BlockList Manager (BLM)
Black Sheep Networks - Information Security contains security guides for Windows, Netware and serveral flavors of UNIX.
Non-CVE vulnerability IDs
OVI - Open Vulnerability ID is a free vulnerability identification number that can be obtained by anyone. Just click below to get your number and use it for your disclosure.
OVE These are unique IDs that you may use to refer to software security vulnerabilities (one ID per vulnerability), much like we use CVE IDs. The difference is that OVE IDs are trivial and quick to obtain, unlike CVE IDs, but as a consequence OVE IDs are issued without any verification, and moreover there's currently no mechanism to reject wrongly assigned/used OVE IDs, nor to merge duplicates.
GitHub - distributedweaknessfiling/DNA-Registry The goal of this project is to allow well-known security researchers and company security teams to assign DWF-style identifiers to security vulnerabilities with minimal overhead.
Blogs
Tools
BackTrack is the most Top rated linux live distribution focused on penetration testing. With no installation whatsoever, the analysis platform is started directly from the CD-Rom and is fully accessible within minutes.
Portknocking
Suites/Applicaties
PacketFence is a Free and Open Source network access control (NAC) system.
Misc
Iomega Zip Disks
Hacker Challenges -- Boon or Bane? Commentary by Gene Spafford, with responses from Sameer Parekh, Jon Wiederspan, and Jeff Weinstein
IEEE Computer Society's Technical Committee on Security and Privacy
Neohapsis
“Lichtelijk offtopic, maar wellicht een leuk weetje.. Met Javascript kan een website uitlezen wat je op je Clipboard(Ctrl+C) hebt staan.. Voorbeeld
Geen bug maar een feature
Denk de volgende keer maar 2 keer na als je aan wachtwoord kopieerd en plakt..”
USB Stick beveiligingsmethoden
Why popular antivirus apps 'do not work'
Eighty percent of new malware defeats antivirus
Why Popular Anti-Virus Apps 'Don't Work'
JavaScript Malware Open The Door to the Intranet
JavaScript vormt toenemend veiligheidsrisico
Known Vulnerabilities in Mozilla Products
Thunderbird 2.0 Alpha 1, Firefox 1.5.0.5 Available
Nieuwe update verhelpt ernstige Firefox-fouten (1.5.0.5)
http://www.firewallleaktester.com/
IT Security Cookbook
Master-Keyed Lock Vulnerability
Is it harmful to discuss security vulnerabilities?
Reflections on Trusting Trust by Ken Thompson
SSLVPN Vulnerabilities - Client Certificates offer a superior defense over OTP devices
SecurityFocus - Analyzing Malicious SSH Login Attempts
dominick baier on .net, security and other stuff
Explaining the “New” TCP Resource Exhaustion Denial of Service (DoS) Attack
[Full-disclosure] Blocking Skype:
The access list then is of the following form :
# Your acl definitions acl numeric_IPs urlpath_regex ^[0-9]+\.[0-9]+\.[0-9]+\.[0-9]+ acl connect method CONNECT # Apply your acls http access deny connect numerics_IPs all
Smashing Magazine - SVN Server Admin Issue: Fix It! .svn directories van productie websites die in SVN worden ontwikkeld zijn in veel gevallen in te zien.
Social Media Security - Exposing the insecurities of social media
Fully Countering Trusting Trust through Diverse Double-Compiling
Mobile Matters - Why Nokia wants my email password? describes how Nokia's e-mail settings wizzard sends your emailaddress and password over HTTPS to their server(s) and asks why.
Mobile Matters - Information about Nokia email case contains instructions to reproduce the tests yourself.
Mobile Matters - Info about the "Nokiagate"
Mobile Matters - Nokia's statement about the Nokiagate
SkullSecurity - Just another security weblog
SkullSecurity - DNS Backdoors with dnscat
SkullSecurity - Weaponizing dnscat with shellcode and Metasploit
SkullSecurity - Wiki - dnscat
PaulDotCom - Cracking MD5 Passwords with BozoCrack “(…)it googles the MD5 hash and hopes the plaintext appears somewhere on the first page of results.”
Coda Hale - How To Safely Store A Password
The Open Web Application Security Project (OWASP)
Secure Programming for Linux and Unix HOWTO -- Creating Secure Software free ebook by David A. Wheeler.
W3C Security Home
UNIX Security
matousec.com is a project run by a group of security experts oriented on desktop users security.
xkcd - Password Strength correct horse battery staple
Beneath the Waves - Motorola Is Listening
Knowledge Brings Fear - Blackberry 10 macht E-Mail-Passworte für NSA und GCHQ zugreifbar
heise online - BlackBerry späht Mail-Login aus
DoctorBeet's Blog - LG Smart TVs logging USB filenames and viewing info to LG servers via Slashdot - User Alleges LG TVs Phone Home With Your Viewing Habits
CloudCracker Blog - Divide and Conquer: Cracking MS-CHAPv2 with a 100% success rate in other words: stop using PPTP.
Helsinki Times - Nokia smartphone leaks information abroad via Slashdot - Lumia Phones Leaking Private Data To Microsoft
Links - Ben Laurie blathering - Who Remembers VASCO?
CIRCL - TR-27 - GNU Bash Critical Vulnerability - CVE-2014-6271 - CVE-2014-7169
Red Hat - Security Blog - Bash specially-crafted environment variables code injection attack
lcamtuf's blog - Quick notes about the bash bug, its impact, and the fixes so far
Ranting for the Revolution! - What's wrong with the kids these days?
EFF - How to Protect Yourself from NSA Attacks on 1024-bit DH
CAPEC-471: DLL Search Order Hijacking
Tweakers.net - Onderzoekers schakelen Intel Management Engine uit via ongedocumenteerde functie
Certificate Authorities
Open Source
Cryptography
Matt Blaze's cryptography resource
Crypto Law Survey by Bert-Jaap Koops
DNS
USB
GitHub - Phison 2251-03 (2303) Custom Firmware & Existing Firmware Patches (BadUSB)
USB Rubber Ducky, GitHub - Payloads
FTP
Keyloggers
Hardware
BIOS/UEFI/Firmware
Mitre - Extreme Privilege Escalation on Windows 8/UEFI Systems presentation. Via Tweakers - Onderzoekers vinden ernstige kwetsbaarheden in uefi
InfoSec Handlers Diary Blog - New Supermicro IPMI/BMC Vulnerability & CARISIRT: Yet Another BMC Vulnerability (And some added extras)
Physical Locks
YouTube - Combo Breaker - motorized combo lock cracking device by Samy Kamkar. Via Tweakers - Hacker automatiseert lockpicking met Arduino-systeem.
YouTube - Break open any Master Combo Lock in 8 tries or less! by Samy Kamkar
Routers
Misfortune Cookie is a critical vulnerability that allows an intruder to remotely take over an Internet router and use it to attack home and business networks.
CPUs
Tweakers - Architectuurfout in oudere x86-cpu's Intel maakt rootkit mogelijk - update
Tweakers - Intels zakelijke processors bevatten al sinds 2008 ernstig lek “ Intels Active Management Technology bevat ernstige kwetsbaarheden waardoor aanvallers de beheerfuncties kunnen gebruiken en zo toegang kunnen krijgen tot hele systemen en netwerken. De kwetsbaarheden zitten in firmwareversies vanaf 2008.”